QKS - Encryption For All The Things
by Keith Elder
TLDR;
Too long? Watch this video on YouTube that explains how QKS was built.
Intro
What do the names Target, Ebay, and Home Depot have in common? Sure they are household names but they are also companies that have had a few of the biggest data breaches in the last few years. Protecting client data is vital to our business. It is the one thing we can control within our systems, but the fact is we haven't had a consistent and centralized way of encrypting client data in the 30 years we've been a company. To apply for a mortgage, our clients must provide very detailed individual and financial information. We as a company must take great precautions to protect that data whether the data is stored internally or within the cloud. QKS, or Quicken Key System solves that problem.

QKS at 100,000 FT
QKS is primarily a centralized key management and sealing service inspired by Amazon's KMS. Here is a sample diagram that is super gumped down as to how it works.
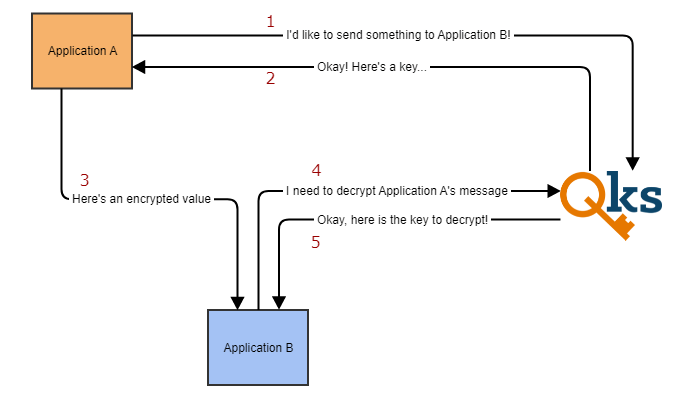
Application A wants to encrypt something and send it to Application B. The first thing each application does is use QKS to generate their initial key. Keys are randomly generated six-digit alphanumeric characters like "A1B2C4". Let's say Application A wants to send the social security number of 123121234 to Application B. System A will make a call to QKS with their key and the receiving key of Application B's. QKS will return some data which instructs Application A how to encrypt the data which would turn the social security number into something like:
ULqBNhKMNh2LGXT2Mnw7x4Gg2G4KOLjP
Application B can then use their six-digit alphanumeric key to call QKS to then reverse the process back into the social security number of 123121234.
This is how QKS works in the simplest form. If you refer to the diagram above the first thing one should notice is client data is NEVER passed to QKS and encrypted or decrypted in QKS itself. Many think that's how it works at first but that could not be further from the truth. The data is always encrypted or decrypted by the application that calls QKS.
What technologies did we use to build QKS?
QKS was written in the Erlang programming language, utilizing the our team's Phoenix platform for building distributed systems. The actual cryptographic operations utilize the Sodium Crypto library (libsodium). By using a really strong crypto library like libsodium, we are able to support multiple programming technologies for today and in the future.
Since July 2013, our team has been doing research and exploration with Erlang. Erlang isn't a new technology stack. It has actually been around since the late 90's and has been used in telecommunications, financial and gaming industries with great success. It is known for building highly scalable, always-on systems. As we looked at the needs of the system we knew whatever we built needed to always be on. And it needed to work all the time and it needed to be able to scale to handle the cloud as well as all the applications internally without a hiccup. And for those reasons we chose to build QKS in Erlang.
Since deploying QKS with Erlang, we have been nothing but short of amazed at the performance and stability of the system. Load tests have been performed on numerous pieces of Rocket Mortgage which call QKS multiple times and it hasn't once faulted.
Sounds amazing! How do I use it?
While QKS exposes a REST for applications to interact with, Engineers do not ever need to interact with the REST API directly. Instead, we've built clients for both .NET and PHP which are available as a nuget package for .NET and a CLU package for PHP.
For .NET and PHP see the links below. Each should provide all the information needed for an Engineer to get started leveraging QKS.
.Net - (redacted)
PHP - (redacted)
Ready... set... protect client data!
Now is a great time to look at your applications where it touches client data, especially PII client data. If it does then you need to encrypt it! Bring this up to your team and get it prioritized. Seriously, every day you don't get the data encrypted we are exposed as a company. The good news is we now have a standardized way for everyone to leverage encryption.
 Portfolio of Keith Elder
Portfolio of Keith Elder